Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
Here you’ll find extensive research and insight from the well-known Horizon3.ai attack team, intuitive perspectives on everything security, and real-world attack path short stories that come directly from discoveries made by NodeZero.
Filters
Showing 1–6 of 418 results
Advancing Emergency Response Security with Autonomous Pentesting
In an increasingly interconnected world, where digital technologies infiltrate every aspect of society, vulnerabilities in these systems can be exploited by malicious actors to disrupt emergency services, compromise sensitive information, or even endanger lives.
Read More 2024 Cloud Security Awards
2024 Cloud Security Awards
Read More 2024 Cybersecurity Excellence Awards
2024 Cybersecurity Excellence Awards
Read More Horizon3.ai Appoints Matt Hartley as Chief Revenue Officer to Spearhead Growth Initiatives
Business Wire 03/25/2024 Horizon3.ai, a leading provider of autonomous security solutions, today announced the appointment of Matt Hartley as Chief Revenue Officer (CRO), effective immediately.Hartley brings over 20 years of sales and operations excellence with a proven track record of building go-to-market (GTM) teams that achieve rapid scale and predictability… Read the entire article here
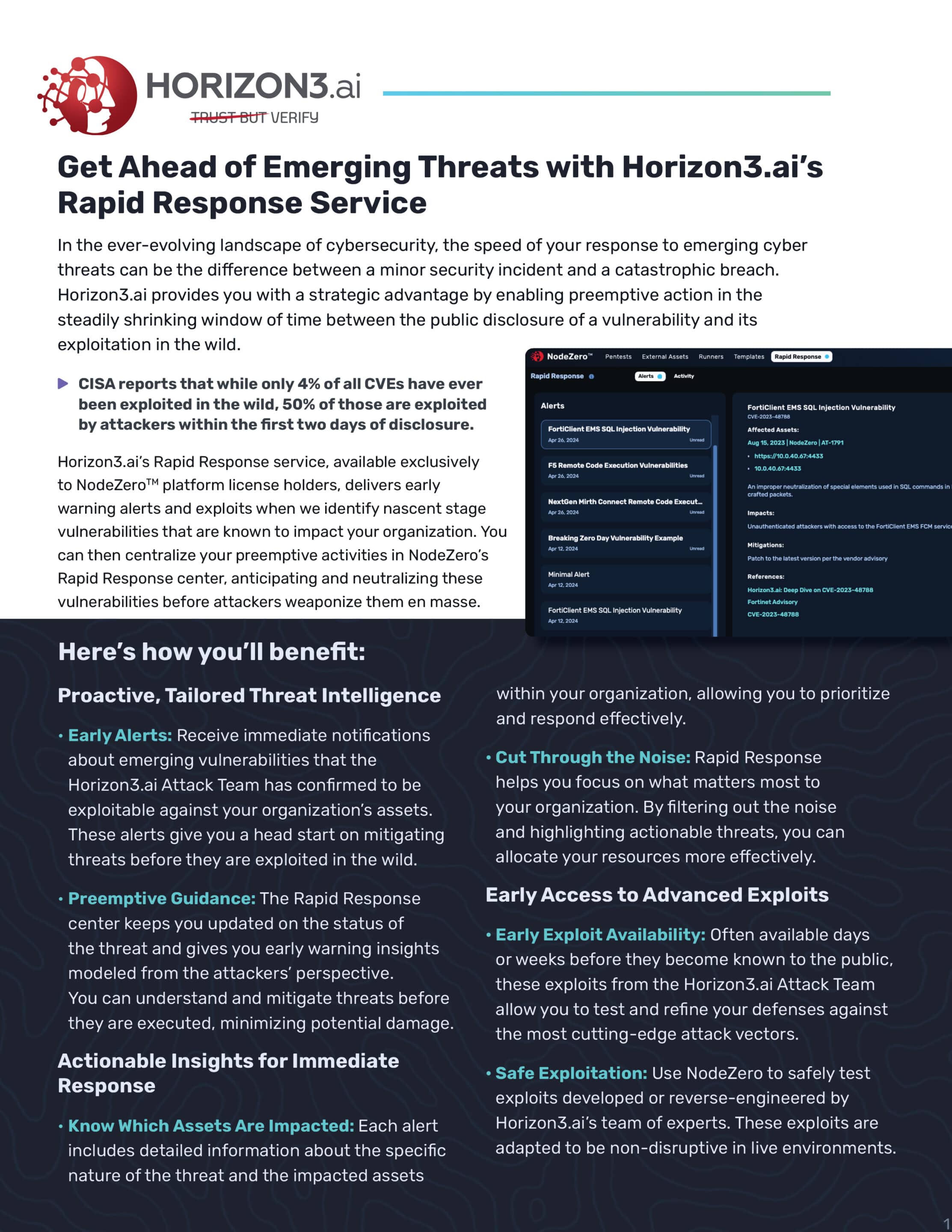
Read More Get Ahead of Emerging Threats with Horizon3.ai’s Rapid Response Service
In the ever-evolving landscape of cybersecurity, the speed of your response to emerging cyber threats can be the difference between a minor security incident and a catastrophic breach. Horizon3.ai provides you with a strategic advantage by enabling preemptive action in the steadily shrinking window of time between the public disclosure of a vulnerability and its exploitation in the wild.
Read More Fix What Matters: Accelerating Cyber Defense Through the Eyes of an Attacker
The emergence of new attack vectors, the steady growth of attack surfaces, and theincreasing speed at which vulnerabilities are exploited underscore the critical needfor proactive defense strategies.
Read More